Free And Confidential Cybersecurity Assessments
This month, we are offering five businesses a free cybersecurity assessment. Complete the form to claim yours today!

What Is a Cybersecurity Risk Assessment?
A cybersecurity risk assessment is a detailed review of your business IT systems, networks, and data practices. The goal is to uncover weaknesses before hackers, malware, or insider threats can take advantage of them. During the assessment, our security experts evaluate how well your systems protect against ransomware, phishing attacks, data breaches, and compliance failures.
By identifying risks early, you can take steps to close security gaps, strengthen backup and recovery plans, and avoid the financial losses that come with downtime or stolen data. Many businesses discover through an assessment that their backups would not fully recover their systems after a ransomware attack or that employee login information is already available on the dark web.
What to Expect From Your Cybersecurity Risk Assessment
After completing your 100% confidential cybersecurity risk assessment, you will know:

Dark Web Exposure
Whether your employees' credentials, passwords, or private information are being sold online.

System Security
If your IT systems and data are truly secured against hackers, malware, and even insider threats.
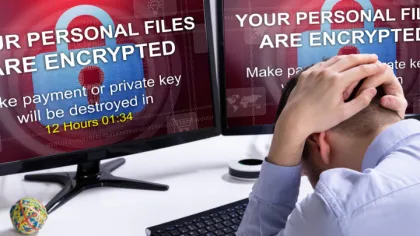
Ransomware Readiness
If your backups would allow you to restore operations quickly after an attack. (99% of the computer networks we've reviewed would NOT survive a ransomware attack.)

Compliance Status
Whether your IT systems, backups, and data handling meet strict compliance and regulatory requirements.

